Access management¶
Afi Backup provides a flexible and granular role model that allows you to:
- configure global (organization-wide) administrators with full or limited access;
- assign per-tenant (data source) administrators and service operators;
- configure granular group-based or per-resource permissions for data access;
- enable limited self-service access for end users for each tenant.
This article focuses on organization-wide access settings that provide high-level access to an entire organization account and all its child tenants.
Global (organization-wide) access¶
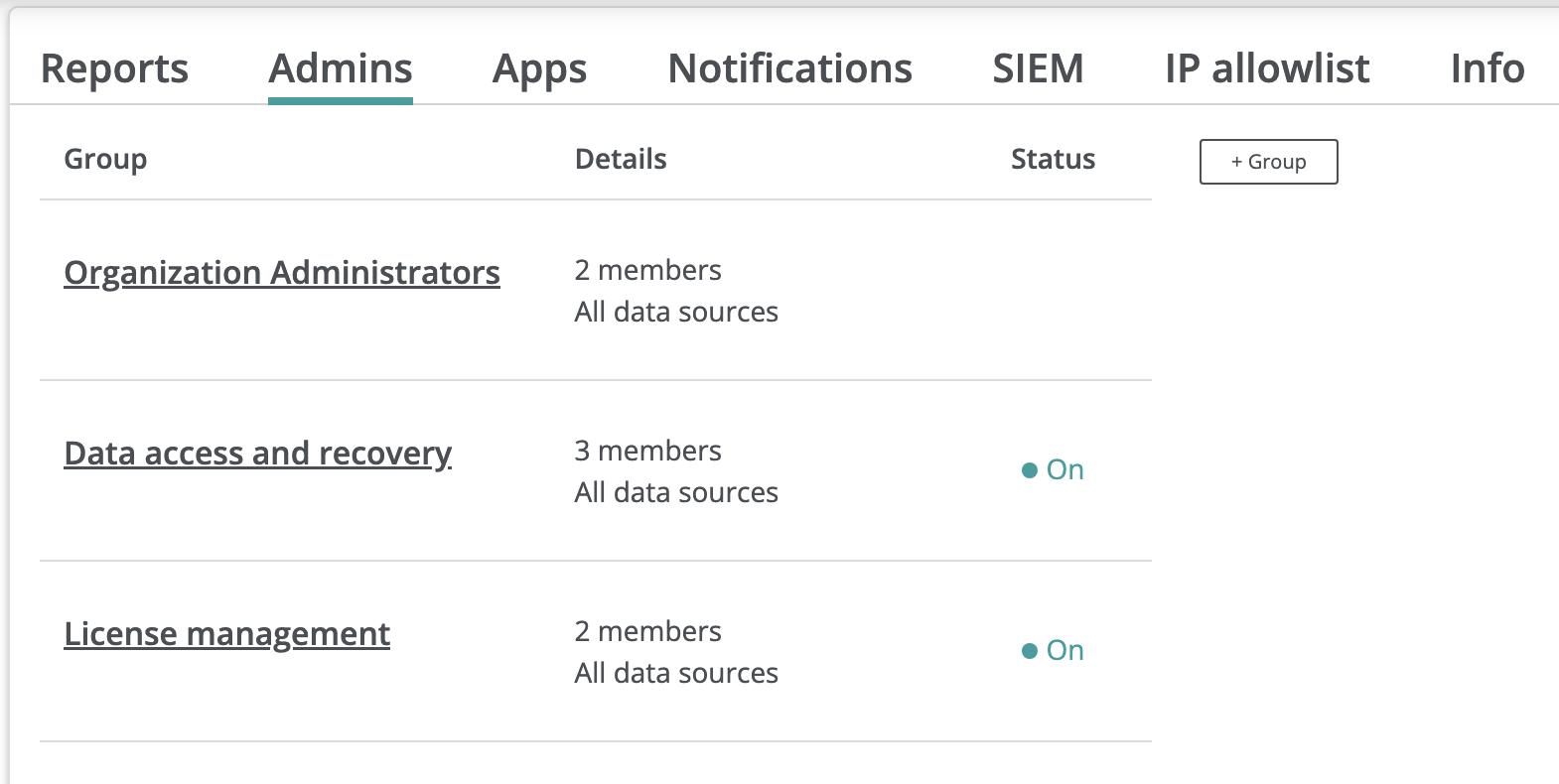
By default, an Afi organization account is created with a single administrator - a Google Workspace or a Microsoft 365 user who has set up the account. Organization administrators are configured on the Configuration → Admins tab and have access to all child tenants (data sources) in the organization. Per data source access can be configured on the Service → Settings → Access groups tab for each tenant as described in the following articles:
- access model and self-service for Google Workspace tenants
- access model and self-service for Microsoft 365 tenants
- access model for Microsoft Azure tenants
- access model for Amazon Web Services tenants
Organization Administrators is a default access group for administrator accounts with full access to an Afi organization account and all its child tenants. We recommend configuring at least two organization administrators for continuous access transition if one of the existing administrators leaves the organization or their account is deleted or unavailable for any reason.
Info
Organization Administrators access to backup data inside the organization's child tenants can be restricted on a per-tenant basis by disabling the corresponding permissions (Browse backup data, Preview email and chats content, Data export) for a tenant inside the Administrators access group on the Service → Settings → Access groups tab. Please note that the Browse backup data permission is required to perform any data recovery activities, but doesn't provide access to email or file content, only to the corresponding metadata.
Custom administrator groups¶
An Afi organization administrator can create additional administrator groups with limited access to the account and its child tenants. A few common use-cases are discussed below.
Info
The application access permissions configured through various access groups for an organization, its child tenants, or custom resource groups are cumulative. This allows a user to be a member of multiple access groups, each with different access settings.
For example, a user can have basic access to browse resources and tasks in all tenants under an organization and, at the same time, can be granted access to perform data export or recovery activities for a specific tenant or a resource group inside a tenant.
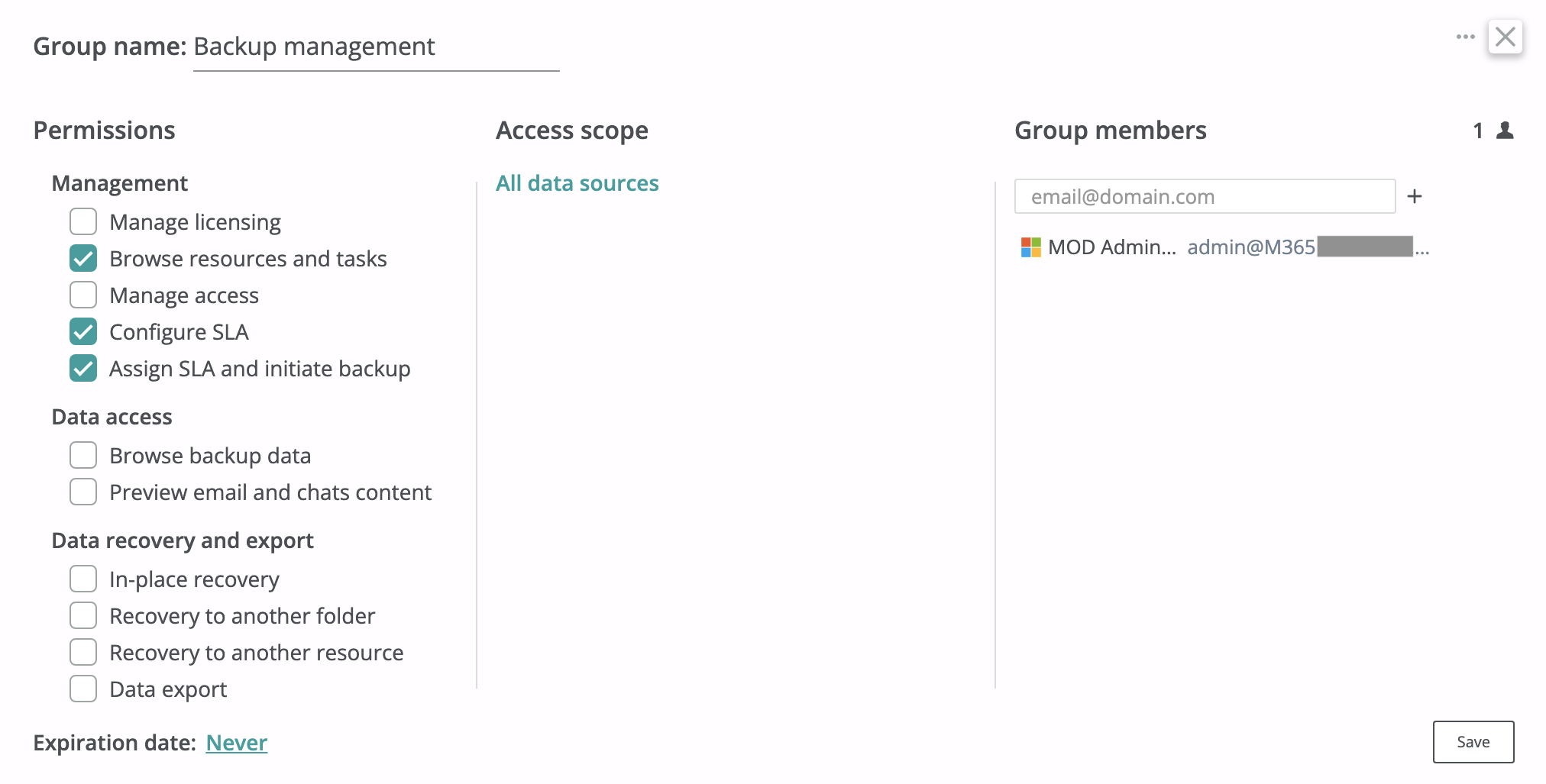
Organization-wide backup management¶
The screenshot below shows how to create a group of administrators who can configure and manage backup SLA policies in each tenant (data source) in the organization account.
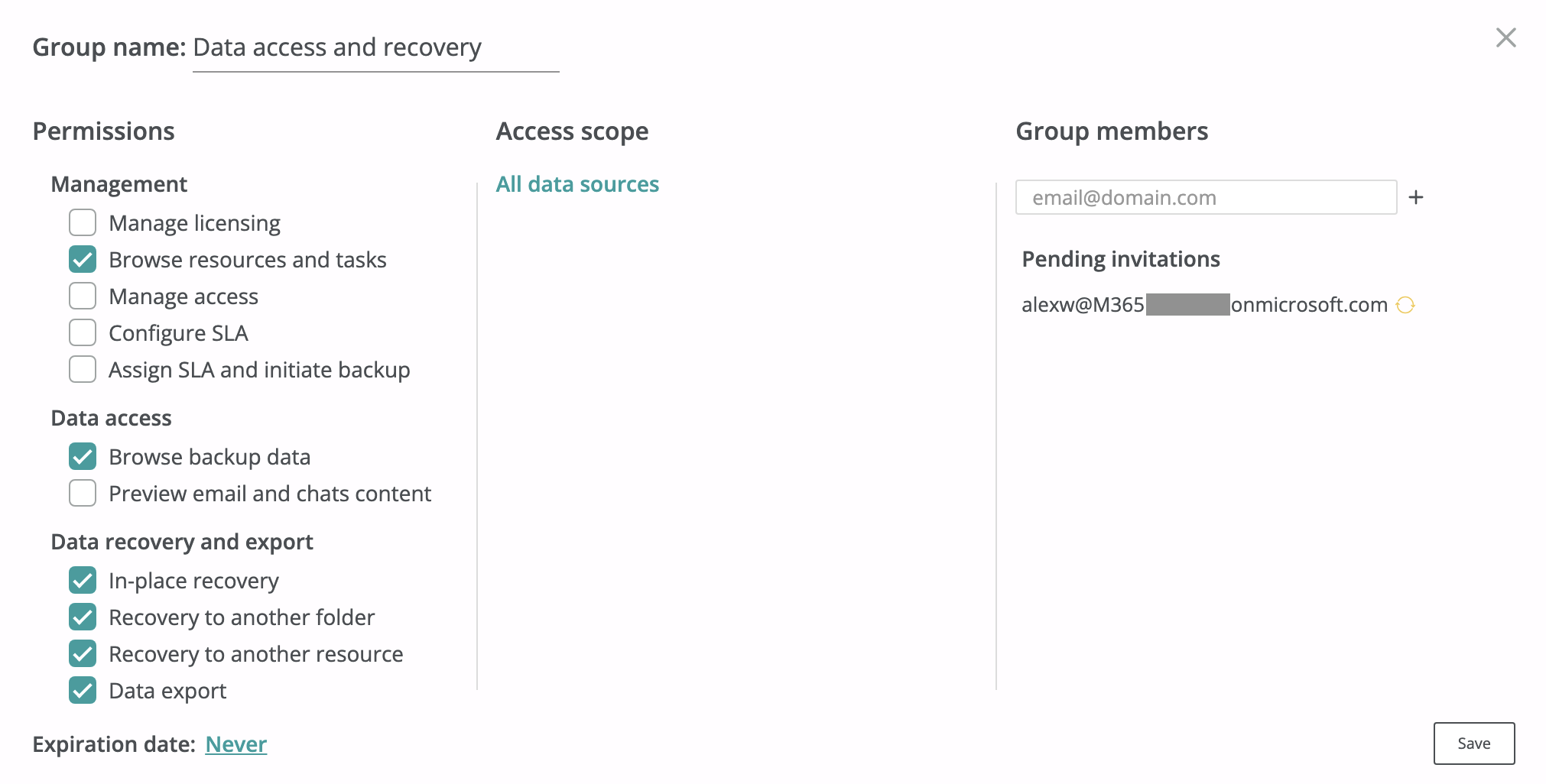
Data access and recovery¶
The screenshot below shows how to create a group of administrators who can export and recover data in each tenant (data source) in the organization account but can't preview email or chat contents during backup browsing.
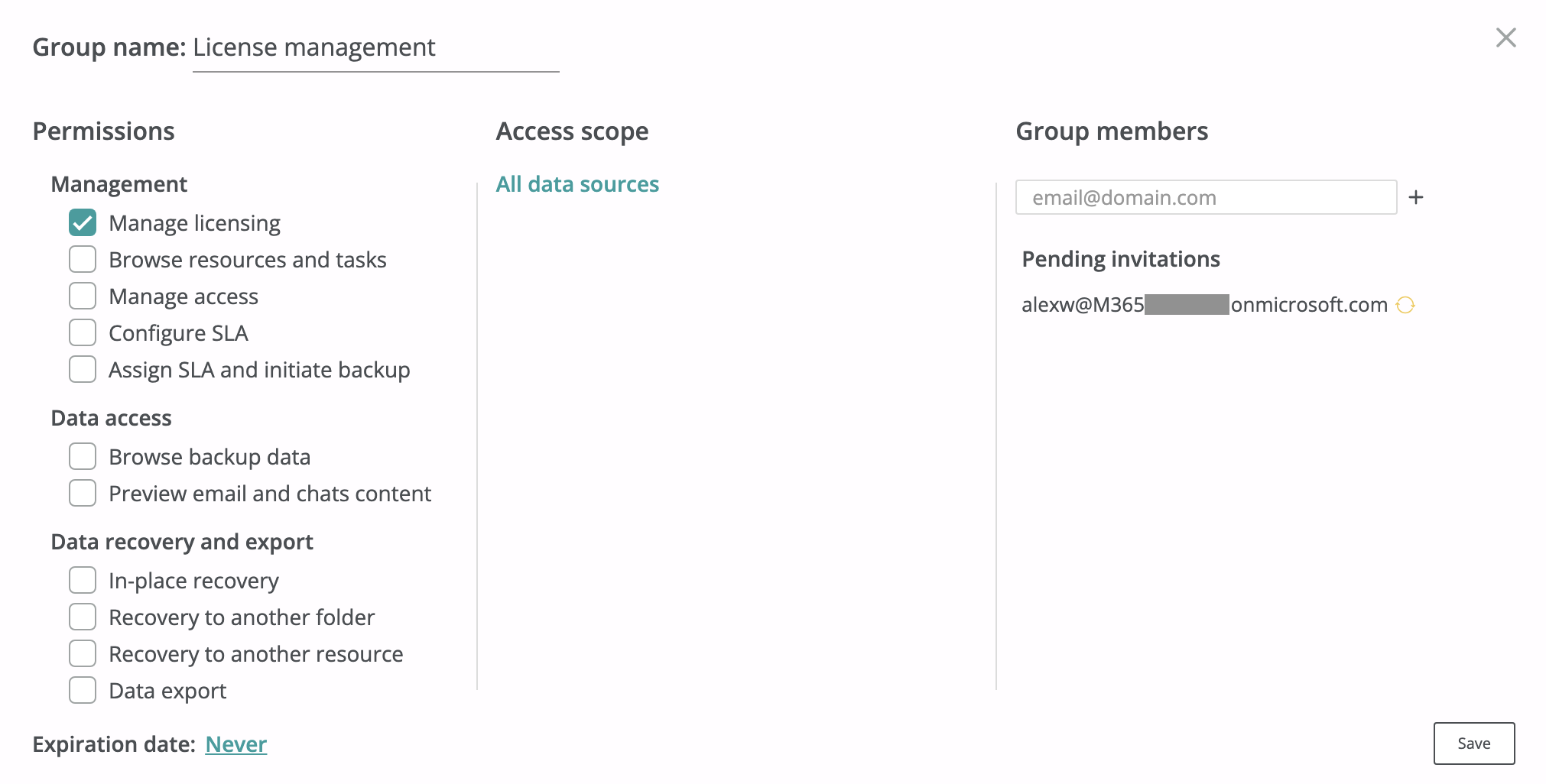
Licensing and billing management¶
The screenshot below shows how to create a group of administrators who can manage service subscriptions for all child tenants within the organization, configure payment options, modify billing details, and view the invoices. The Manage licensing permission doesn't provide any access to backup data or organization/tenant settings management.
How to invite a member to a group?¶
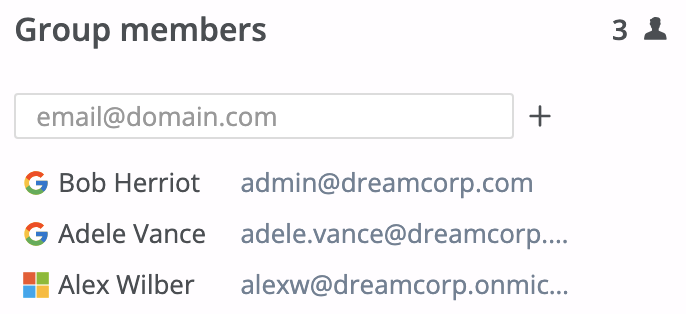
An Afi organization administrator can invite a user to an organization-level access group (including the default Organization Administrators group) by clicking on the group tile, posting the primary user email in the input field in the Group members section, clicking on the + icon, and then pressing Save.
After a user is invited, the Afi service sends an email invitation to that user to join the corresponding access group by using the link provided in the email. Each link is valid for 7 days and, once you delete and add a user to this group again, the old invitation link becomes invalid. To join the group, the user should follow the link and log in to the Afi portal with the account specified in the invitation.
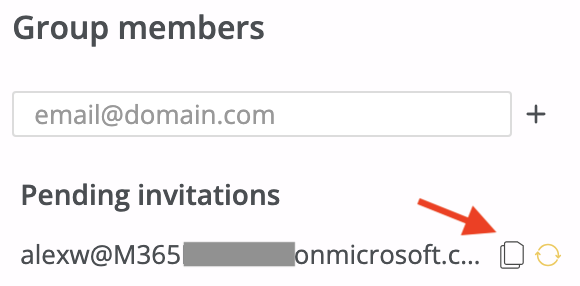
If an invited user doesn't have an active mailbox and can't receive an email invitation, please provide the user with the invitation link from the access group settings dialog. You can copy the link by clicking the Copy icon for the corresponding email in the Pending invitations section.
Once a user has accepted the invitation, the service links their Google Workspace or Microsoft 365 account, which was used to accept the invitation, to the corresponding access group.
If a user tries to accept an invitation with a non-matching account with a different primary email address, the invitation won't be accepted and the user should try again with the matching account.
Info
Please note that Afi identifies users by their Google Workspace or Microsoft 365 unique identifiers and not by email. So, if a user has both Google Workspace and Microsoft 365 user accounts with the same email, these are different accounts from the Afi point of view and such accounts don't share the same access settings.
The same way, if an administrator deleted their old Google Workspace/Microsoft 365 user account and created a new one with the same email, it will be a different account from the Afi point of view and it should be invited again to manage the Afi service by existing Afi account administrators.
Afi doesn't require administrator users to come from the organization's child tenants, so any user with a Google account (personal or business/educational) or a Microsoft 365 business account can be invited. This way, you can add a user from outside your Google Workspace or Microsoft 365 tenant for emergency access to the Afi account. You can also invite users from a new Google Workspace or Microsoft 365 tenant if your organization moved to another tenant and wants to keep the old backup data archived with Afi.
Permissions explained¶
Management¶
| Permission | Description |
|---|---|
| Manage licensing | An access group member can manage service subscriptions for all child tenants within the organization, configure payment options, modify billing details, and view the invoices. |
| Add new data sources | An access group member can add new data sources (tenants) under the organization account. |
| Add new customers | An access group member can add customers organizations under the partner account. This permission is available only for partner organizations. |
| Browse resources and tasks | An access group member can see a list of resources and their protection statuses as well as check backup activity for all child tenants within the organization, but can't manage or access the backups without additional permissions. |
| Manage access | An access group member is able to change access settings within the organization and all its child tenants by creating new access groups or editing settings and members for existing ones. |
| Manage organization access policies | An access group member is able to change access policies within the organization. Access policies available for configuration include organization access rules based on IP address, country, and identity provider, as well as lockdown mode for sensitive operations restriction. |
| Configure SLA | An access group member is able to create, modify or delete backup SLA policies within all child tenants on the Service → Settings → SLA tab. |
| Assign SLA and initiate backup | An access group member is able to assign backup SLA policies to resources within all child tenants and configure auto-protection settings. |
Data access¶
| Permission | Description |
|---|---|
| Browse backup data | An access group member is able to browse backup data, but can't export the data or preview email and chats content without additional permissions. |
| Preview content | An access group member is able to see content for backed up items (emails, chat messages, virtual machine volumes, database tables, etc.). |
Data recovery and export¶
| Permission | Description |
|---|---|
| In-place recovery | An access group member can trigger a recovery operation that restores all selected items (for example, emails/files) from a backup to the same resource and to the same paths where they were during a backup. This recovery mode should be used with caution as it will overwrite files if they have been changed since the time when the backup was done. |
| Recovery to another folder | An access group member is able to recover backup data to a separate folder/location inside a restore destination resource. This is the safest recovery option which guarantees that no data will be accidentally overwritten. |
| Recovery to another resource | An access group member is able to recover backup data to another resource. This option is enabled together with one of the following options: Recovery to another folder (default) or In-place recovery. |
| Data export | An access group member is able to download backup data from all backups in the group's access scope. |